[ad_1] As working professionals and students who value our privacy in today’s digital world, many of us rely on VPN services to secure our online activities and locations. However, it is inevitable that sometimes one needs to disable VPN access, perhaps for certain apps that... Continue reading
[ad_1] OWASP discloses a data breach Pierluigi Paganini April 01, 2024 The OWASP Foundation disclosed a data breach that impacted some members due to a misconfiguration of an old Wiki web server. The OWASP Foundation has disclosed a data breach that impacted some of its... Continue reading
[ad_1] Pentagon established the Office of the Assistant Secretary of Defense for Cyber Policy Pierluigi Paganini April 01, 2024 The US government announced establishing the Office of the Assistant Secretary of Defense for Cyber Policy. The US Defense Department announced establishing the Office of the... Continue reading
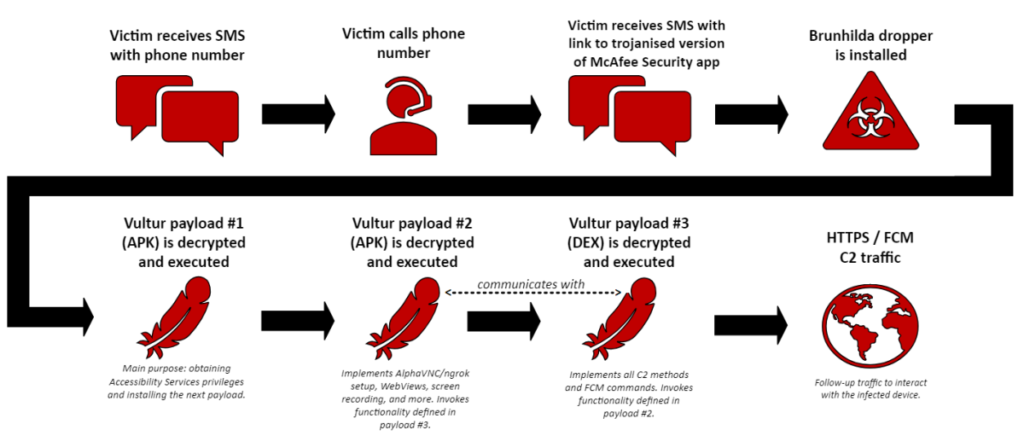
[ad_1] New Vultur malware version includes enhanced remote control and evasion capabilities Pierluigi Paganini April 01, 2024 Researchers detected a new version of the Vultur banking trojan for Android with enhanced remote control and evasion capabilities. Researchers from NCC Group discovered a new version of... Continue reading
[ad_1] By Mr. Zakir Hussain, CEO – BD Software Distribution As digital landscapes morph and expand, cybersecurity challenges intensify. The fusion of digital advancement, the adoption of hybrid workplaces, and the transition towards cloud-based operations are not only widening the threat horizons but also exposing... Continue reading
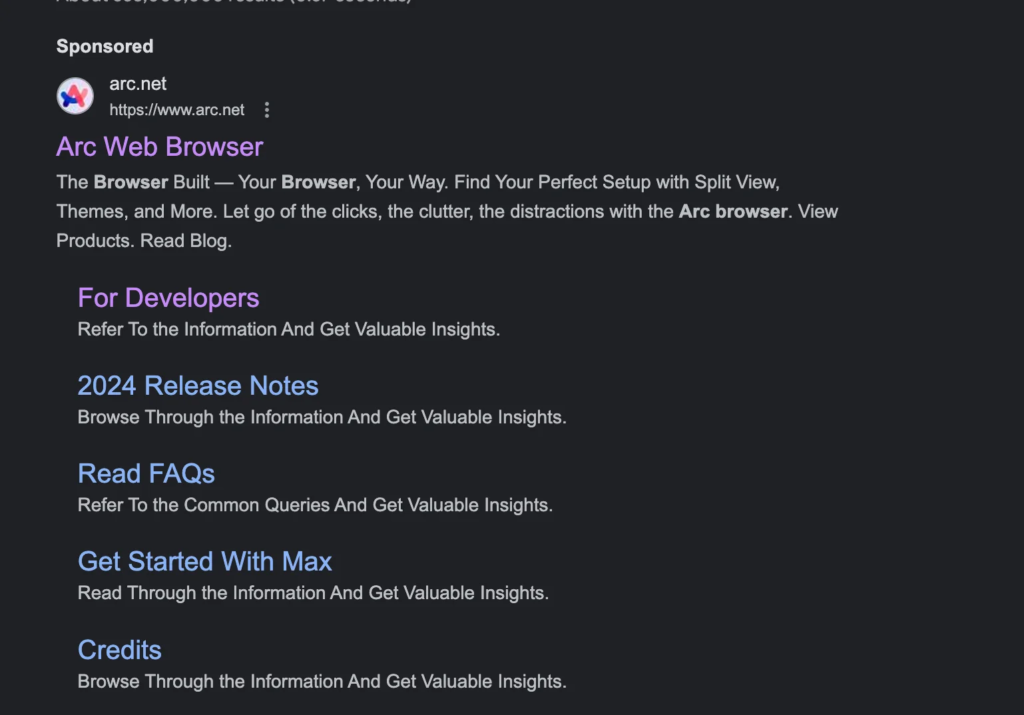
[ad_1] Info stealer attacks target macOS users Pierluigi Paganini April 01, 2024 Experts warn of info stealer malware, including Atomic Stealer, targeting Apple macOS users via malicious ads and rogue websites. Jamf Threat Labs researchers analyzed info stealer malware attacks targeting macOS users via malicious... Continue reading
[ad_1] Telecommunications giant AT&T has confirmed a data breach affecting 73 million accounts. The company’s official press release confirms the AT&T data breach stating several facts and figures about the incident. The AT&T data leak came to light when it was discovered that a substantial... Continue reading
[ad_1] In an era where phone calls seemed to be on the decline, scammers proved otherwise by inundating our cell phones with relentless calls, employing deceitful tactics to extract information and money from unsuspecting victims. Initially perceived as a modern-day nuisance akin to telemarketers, these... Continue reading
[ad_1] DinodasRAT Linux variant targets users worldwide Pierluigi Paganini March 31, 2024 A Linux variant of the DinodasRAT backdoor used in attacks against users in China, Taiwan, Turkey, and Uzbekistan, researchers from Kaspersky warn. Researchers from Kaspersky uncovered a Linux version of a multi-platform backdoor DinodasRAT that was employed... Continue reading
[ad_1] Imagine this: a spreadsheet holding your company’s financial secrets, a client list with confidential contact details, or even a personal budget with sensitive information. Suddenly, a shiver runs down your spine as you realize that anyone with access to your computer could peek into... Continue reading