[ad_1] Sensitive Swiss federal government data, including classified documents and log in credentials, were leaked by the Play ransomware group following an attack on IT service provider Xplain in 2023. An investigation by Switzerland’s National Cyber Security Centre (NCSC) revealed that around 65,000 documents relating... Continue reading
[ad_1] CISA adds Apple iOS and iPadOS memory corruption bugs to its Known Exploited Vulnerabilities Catalog Pierluigi Paganini March 07, 2024 U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Apple iOS and iPadOS memory corruption vulnerabilities to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity... Continue reading
[ad_1] A threat actor has been distributing remote access Trojans (RATs) on Android and Windows operating systems using online meeting lures, according to cloud security provider Zscaler. This campaign has been ongoing since at least December 2023, observed Zscaler’s threat intelligence team, ThreatLabz. The distributed... Continue reading
[ad_1] The European Union (EU) has agreed new rules to strengthen cyber incident response and recovery across member states, which has been dubbed the ‘cyber solidarity act.’ The provisional regulation aims to make the EU more resilient and reactive to cyber threats via new cooperation... Continue reading
[ad_1] LockBit 3.0’s Bungled Comeback Highlights the Undying Risk of Torrent-Based (P2P) Data Leakage Pierluigi Paganini March 06, 2024 The wide torrent-based accessibility of these leaked victim files ensures the longevity of LockBit 3.0’s harmful impact. While embattled ransomware gang LockBit 3.0 fights for its... Continue reading
[ad_1] Security researchers have uncovered an emerging malware campaign targeting misconfigured servers hosting web-facing services like Apache Hadoop YARN, Docker, Confluence and Redis. This campaign is notable for employing novel Golang payloads designed to automate the identification and exploitation of vulnerable hosts. According to an... Continue reading
[ad_1] CISA ADDS ANDROID PIXEL AND SUNHILLO SURELINE BUGS TO ITS KNOWN EXPLOITED VULNERABILITIES CATALOG Pierluigi Paganini March 06, 2024 U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Android Pixel and Sunhillo SureLine vulnerabilities to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure... Continue reading
[ad_1] The TA4903 group has been observed engaging in extensive spoofing of both US government agencies and private businesses across various industries. While primarily targeting organizations within the United States, TA4903 occasionally extends its reach globally through high-volume email campaigns. The overarching objective of these campaigns,... Continue reading
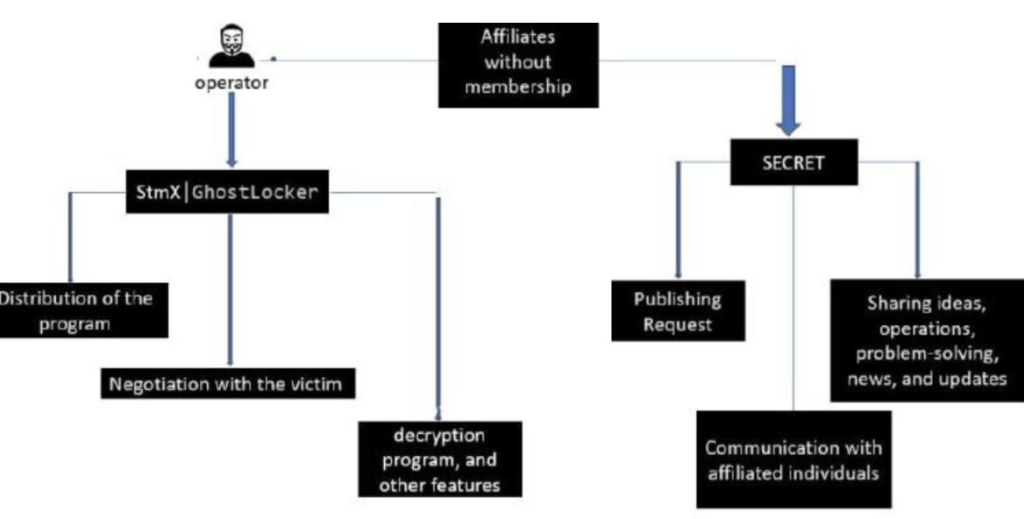
[ad_1] Watch out, GhostSec and Stourmous groups jointly conducting ransomware attacks Pierluigi Paganini March 06, 2024 Researchers warn that the cybercrime groups GhostSec and Stormous have joined forces in a new ransomware campaign. The GhostSec and Stormous ransomware gang are jointly conducting a ransomware campaign... Continue reading
[ad_1] Cybersecurity professionals are increasingly prepared to moonlight as cybercriminals in a bid to top up their salaries, according to new research from the Chartered Institute of Information Security (CIISec). The institute enlisted the help of a former police officer and covert operative to analyze... Continue reading