[ad_1] Nation-state actors are using AI services and LLMs for cyberattacks Pierluigi Paganini February 15, 2024 Microsoft and OpenAI warn that nation-state actors are using ChatGPT to automate some phases of their attack chains, including target reconnaissance and social engineering attacks. Multiple nation-state actors are... Continue reading
[ad_1] Just over $22bn worth of cryptocurrency was laundered in 2023, a 30% drop from the previous year, with nefarious actors switching techniques to stay hidden from investigators, according to Chainalysis. The blockchain analysis company claimed in a new report that some of the decline... Continue reading
[ad_1] CISA adds Microsoft Windows bugs to its Known Exploited Vulnerabilities catalog Pierluigi Paganini February 15, 2024 U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds 2 Microsoft Windows flaws to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the following... Continue reading
[ad_1] Security researchers have warned of a sophisticated new Trojan designed to steal facial biometric data and use it to produce deepfakes of victims which can bypass banking logins. Group-IB said the GoldPickaxe malware is available for Android and iOS, and developed by a suspected Chinese cybercrime actor... Continue reading
[ad_1] Zoom fixed critical flaw CVE-2024-24691 in Windows software Pierluigi Paganini February 14, 2024 Zoom addressed seven vulnerabilities in its desktop and mobile applications, including a critical flaw (CVE-2024-24691) affecting the Windows software. The popular Video messaging giant Zoom released security updates to address seven... Continue reading
[ad_1] Cybersecurity spending is predicted to be cut by 41% of SMEs over the coming year amid the challenging economic environment, according to new research by JumpCloud. Nearly three-quarters (72%) of IT admins surveyed in the US, UK and India agreed that any cuts to... Continue reading
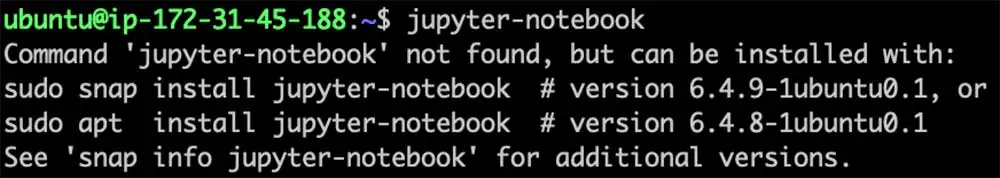
[ad_1] Abusing the Ubuntu ‘command-not-found’ utility to install malicious packages Pierluigi Paganini February 14, 2024 Researchers reported that attackers can exploit the ‘command-not-found’ utility to trick users into installing rogue packages on Ubuntu systems. Cybersecurity researchers from cloud security firm Aqua discovered that it is... Continue reading
[ad_1] A substantial 55% of recent Data Loss Prevention (DLP) events have involved attempts to input personally identifiable information (PII), while 40% included confidential documents. The figures come from Menlo Security’s report The Continued Impact of Generative AI on Security Posture, published earlier today. According... Continue reading
[ad_1] In the office of the Manhattan Property Clerk, evidence and lost items arrive by the tens of thousands. A small band of officers and civilians has to manage never-ending pressure. Feb. 14, 2024 Charmain Carryl moved with purpose through the dim, cavernous room. She... Continue reading
[ad_1] The Trend Micro Zero Day Initiative (ZDI) has recently unearthed a critical vulnerability, identified as CVE-2024-21412, which they’ve dubbed ZDI-CAN-23100. The flaw was reported to Microsoft as part of a Microsoft Defender SmartScreen bypass utilized in a complex zero-day attack chain orchestrated by the... Continue reading