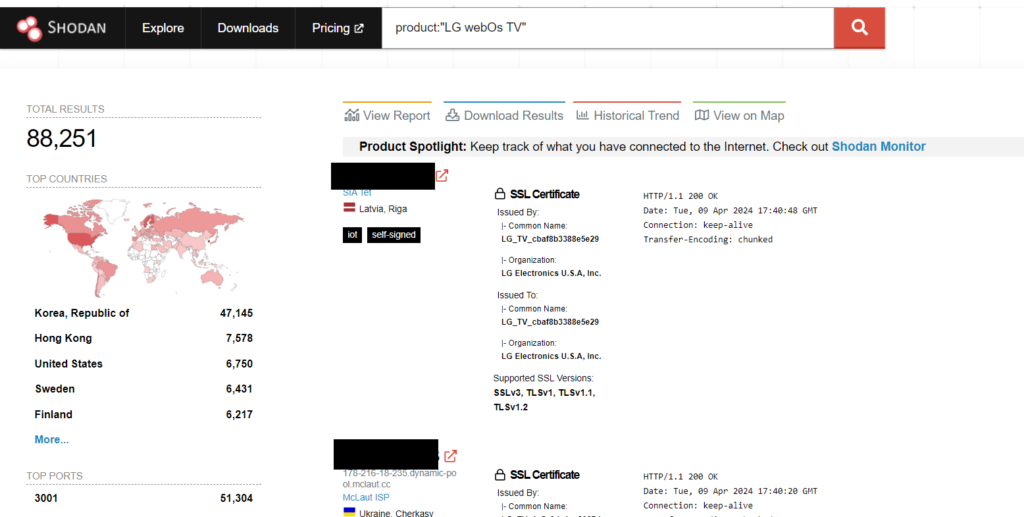
[ad_1] Over 91,000 LG smart TVs running webOS are vulnerable to hacking Pierluigi Paganini April 09, 2024 Researchers found multiple vulnerabilities in LG webOS running on smart TVs that could allow attackers to gain root access to the devices. Bitdefender researchers discovered multiple vulnerabilities in... Continue reading
[ad_1] Many threat actors are turning to malware to scan software vulnerabilities that they can use in future cyber-attacks. Security researchers at Unit 42, the threat intelligence branch of cybersecurity provider Palo Alto Networks, discovered a significant number of malware-initiated scans among the scanning attacks... Continue reading
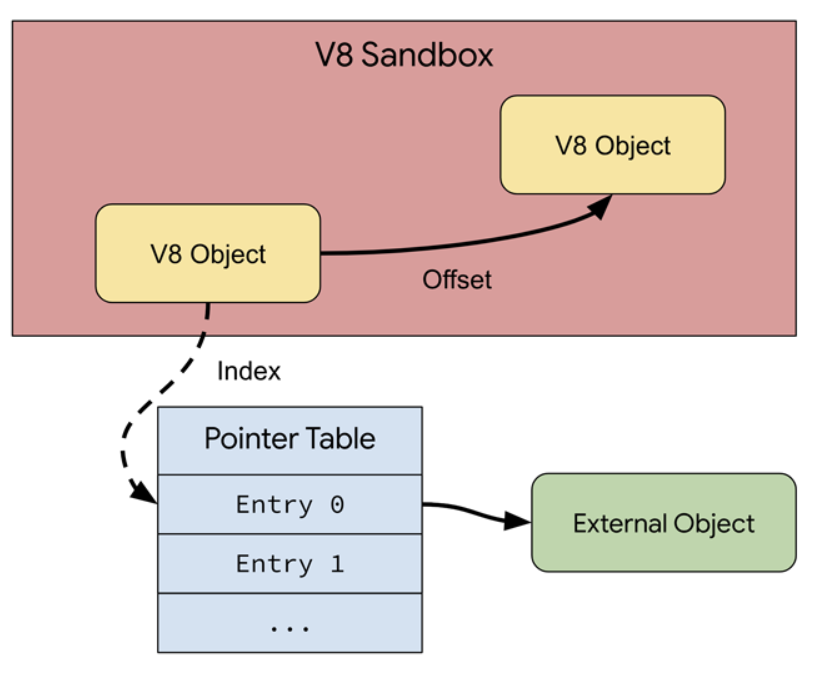
[ad_1] Google announces V8 Sandbox to protect Chrome users Pierluigi Paganini April 09, 2024 Google announced support for a V8 Sandbox in the Chrome web browser to protect users from exploits triggering memory corruption issues. Google has announced support for what’s called a V8 Sandbox in the Chrome web... Continue reading
[ad_1] Hostile foreign states are behind a surge in malicious insider breaches, driving IP theft and industrial espionage to an all-time high, according to DTEX. The insider threat specialist analyzed over 1300 investigations across its global customer base to compile the 2024 i3 Insider Risk Investigations... Continue reading
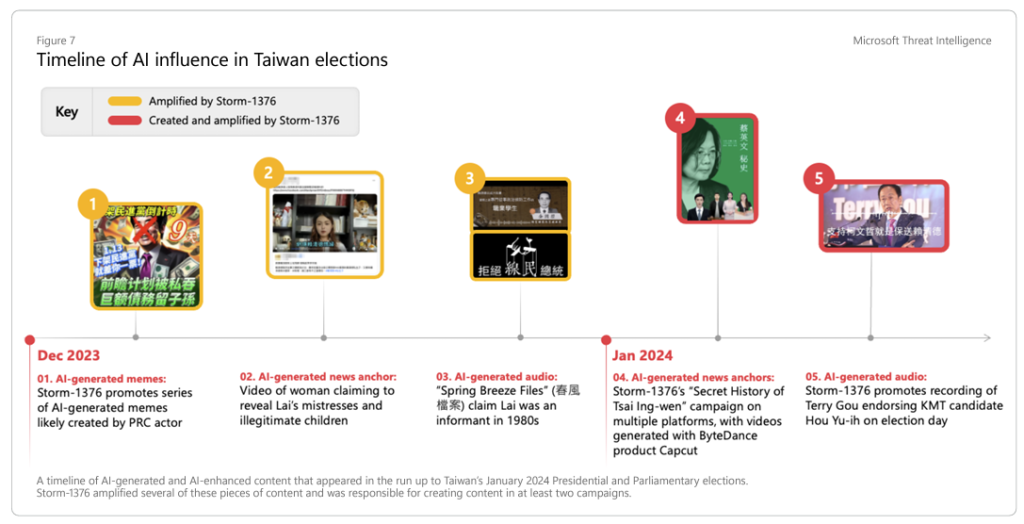
[ad_1] China is using generative AI to carry out influence operations Pierluigi Paganini April 09, 2024 China-linked threat actors are using AI to carry out influence operations aimed at fueling social disorders in the U.S. and Taiwan. China is using generative artificial intelligence to carry... Continue reading
[ad_1] Identity compromise is one of the top cyber threats to organizations, prompting cybersecurity professionals to encourage better identity management hygiene across industries. According to the Identity Defined Security Alliance (IDSA), almost nine out of ten businesses (84%) have experienced an identity-related breach over the... Continue reading
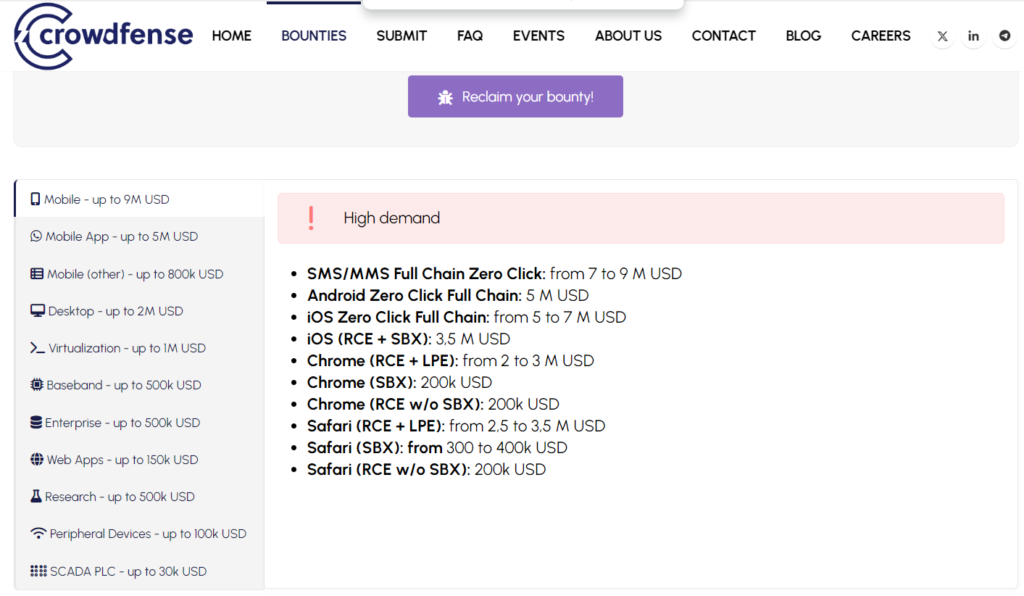
[ad_1] Crowdfense is offering a larger 30M USD exploit acquisition program Pierluigi Paganini April 08, 2024 Zero-day broker firm Crowdfense announced a 30 million USD offer as part of its Exploit Acquisition Program. Crowdfense is a world-leading research hub and acquisition platform focused on high-quality... Continue reading
[ad_1] Cybersecurity researchers have identified a new loader named “Latrodectus,” discovered in November 2023, which has since been associated with nearly a dozen campaigns since February 2024. This malware, described in an advisory published by Proofpoint last Thursday, was primarily utilized by actors identified as... Continue reading
[ad_1] Greylock McKinnon Associates data breach exposed DOJ data of 341650 people Pierluigi Paganini April 08, 2024 Greylock McKinnon Associates, a service provider for the Department of Justice, suffered a data breach that exposed data of 341650 people. Greylock McKinnon Associates (GMA) provides expert economic... Continue reading
[ad_1] New research has shed light on the intricate workings of the Byakugan malware, initially detected in January. During an investigation into a campaign featuring malware concealed within PDFs, the FortiGuard Labs team unearthed additional insights about the malware. Last Thursday, they issued an advisory... Continue reading