[ad_1] Scams The AI race is on! It’s easy to lose track of the latest developments and possibilities, and yet everyone wants to see firsthand what the hype is about. Heydays for cybercriminals! 21 Aug 2023 • , 4 min. read My first “huh?” moment... Continue reading
[ad_1] Secure Coding, Business Security Or, is mass public meddling just opening the door for problems? And how does open-source software compare to proprietary software in terms of security? 26 Sep 2023 • , 5 min. read There are – and will always be –... Continue reading
[ad_1] Secure Coding While far from all roles in security explicitly demand coding skills, it’s challenging to envision a career in this field that wouldn’t derive substantial advantages from at least a basic understanding of fundamental coding principles 27 Sep 2023 • , 4 min.... Continue reading
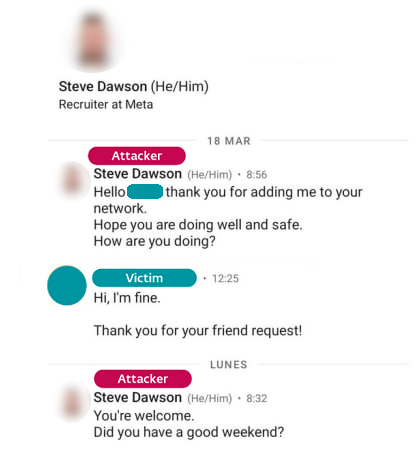
[ad_1] ESET researchers have uncovered a Lazarus attack against an aerospace company in Spain, where the group deployed several tools, most notably a publicly undocumented backdoor we named LightlessCan. Lazarus operators obtained initial access to the company’s network last year after a successful spearphishing campaign,... Continue reading
[ad_1] Video During the attack, the group deployed several tools, most notably a newly-discovered sophisticated backdoor that ESET named LightlessCan 29 Sep 2023 This week, ESET researchers unveiled their findings about an attack by the North Korea-linked APT group Lazarus that took aim at an... Continue reading
[ad_1] Google has patched three high-severity flaws in the latest release of its Chrome browser, including one zero-day vulnerability it said is being actively exploited in the wild. Google Chrome 117.0.5938.132 is currently rolling out worldwide to Windows, Mac and Linux users in the Stable desktop... Continue reading
[ad_1] Progress Software has urged customers to patch a critical new vulnerability in one of its flagship file transfer software products, which could impact thousands of customers worldwide. The software company is more famous for MOVEit, a managed file transfer offering which was recently exploited... Continue reading
[ad_1] A sophisticated Chinese cyber-espionage campaign targeting Microsoft Outlook accounts gave Beijing access to tens of thousands of private US government emails, according to a new report. The Storm-0558 group was able to steal 60,000 emails from 10 State Department accounts, nine of which were... Continue reading
[ad_1] Recent weeks have witnessed a significant increase in cyber-attacks targeting the US Postal Service (USPS), mainly through phishing and smishing campaigns. The surge in these attacks has prompted DomainTools researchers to delve into their origins and implications, with findings described in an advisory published... Continue reading
[ad_1] Microsoft’s Bing Chat has come under scrutiny due to a significant security concern – the infiltration of malicious ads. Malwarebytes researchers have now demonstrated how unsuspecting users seeking software downloads can be tricked into visiting malicious websites and unwittingly downloading malware. Bing Chat, an... Continue reading