[ad_1] Digital Security As fabricated images, videos and audio clips of real people go mainstream, the prospect of a firehose of AI-powered disinformation is a cause for mounting concern 13 Feb 2024 • , 5 min. read Fake news has dominated election headlines ever since... Continue reading
[ad_1] Ukrainian national faces up to 20 years in prison for his role in Zeus, IcedID malware schemes Pierluigi Paganini February 17, 2024 A Ukrainian national pleaded guilty to his role in the Zeus and IcedID operations, which caused tens of millions of dollars in... Continue reading
[ad_1] Video Here’s how the results of vulnerability scans factor into decisions on cyber-insurance and how human intelligence comes into play in the assessment of such digital signals 16 Feb 2024 Cyber-insurance has been an increasingly hot topic lately, with the cyber-insurance industry growing of... Continue reading
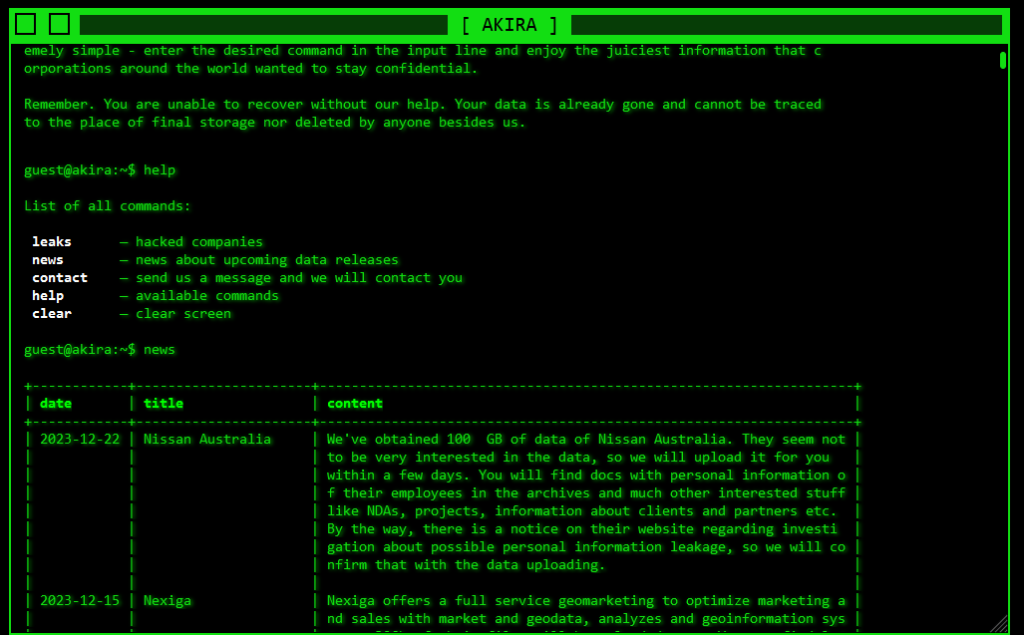
[ad_1] CISA: Cisco ASA/FTD bug CVE-2020-3259 exploited in ransomware attacks Pierluigi Paganini February 17, 2024 CISA warns that the Akira Ransomware gang is exploiting the Cisco ASA/FTD vulnerability CVE-2020-3259 (CVSS score: 7.5) in attacks in the wild. This week the U.S. Cybersecurity and Infrastructure Security Agency (CISA)... Continue reading
[ad_1] The burgeoning field of digital forensics plays a crucial role in investigating a wide range of cybercrimes and cybersecurity incidents. Indeed, in our technology-centric world, even investigations of ‘traditional’ crimes often include an element of digital evidence that is waiting to be retrieved and... Continue reading
[ad_1] Video Artificial intelligence is on everybody’s lips these days, but there are also many misconceptions about what AI actually is and isn’t. We unpack the basics and examine AI’s broader implications. 15 Feb 2024 Artificial intelligence (AI) is clearly the topic du jour as... Continue reading
[ad_1] US gov offers a reward of up to $10M for info on ALPHV/Blackcat gang leaders Pierluigi Paganini February 16, 2024 The U.S. government offers rewards of up to $10 million for information that could lead to the identification or location of ALPHV/Blackcat ransomware gang leaders.... Continue reading
[ad_1] Google has called for a balanced regulatory approach to AI in order to avoid a future where attackers can innovate but defenders are stifled by law. Google’s call comes following the launch of a new whitepaper “Secure, Empower, Advance: How AI Can Reverse the... Continue reading
[ad_1] CISA adds Microsoft Exchange and Cisco ASA and FTD bugs to its Known Exploited Vulnerabilities catalog Pierluigi Paganini February 16, 2024 U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Microsoft Exchange and Cisco ASA and FTD bugs to its Known Exploited Vulnerabilities catalog. The... Continue reading
[ad_1] Organizations based in the EU are being targeted by spear phishing campaigns leveraging EU political and diplomatic events, according to the bloc’s Computer Emergency Response Team (CERT-EU). In its Threat Landscape Report 2023, published on February 15, 2024, CERT-EU found that lures exploiting the... Continue reading